hello friends! new(ish)!
Setting up a Server: Difference between revisions
>WubTheCaptain ({{Move}}) |
>WubTheCaptain (Merged {{Move}}) |
||
| Line 1: | Line 1: | ||
{{Move||[[wikipedia:Wikipedia:Naming_conventions (capitalization)]]. Title makes it unclear which server we're talking about. Remember [[Special:WhatLinksHere/Setting_up_a_Server]]}} | {{Move||[[wikipedia:Wikipedia:Naming_conventions (capitalization)]]. Title makes it unclear which server we're talking about. Merge with [[Home server]] suggested. Remember [[Special:WhatLinksHere/Setting_up_a_Server]]}} | ||
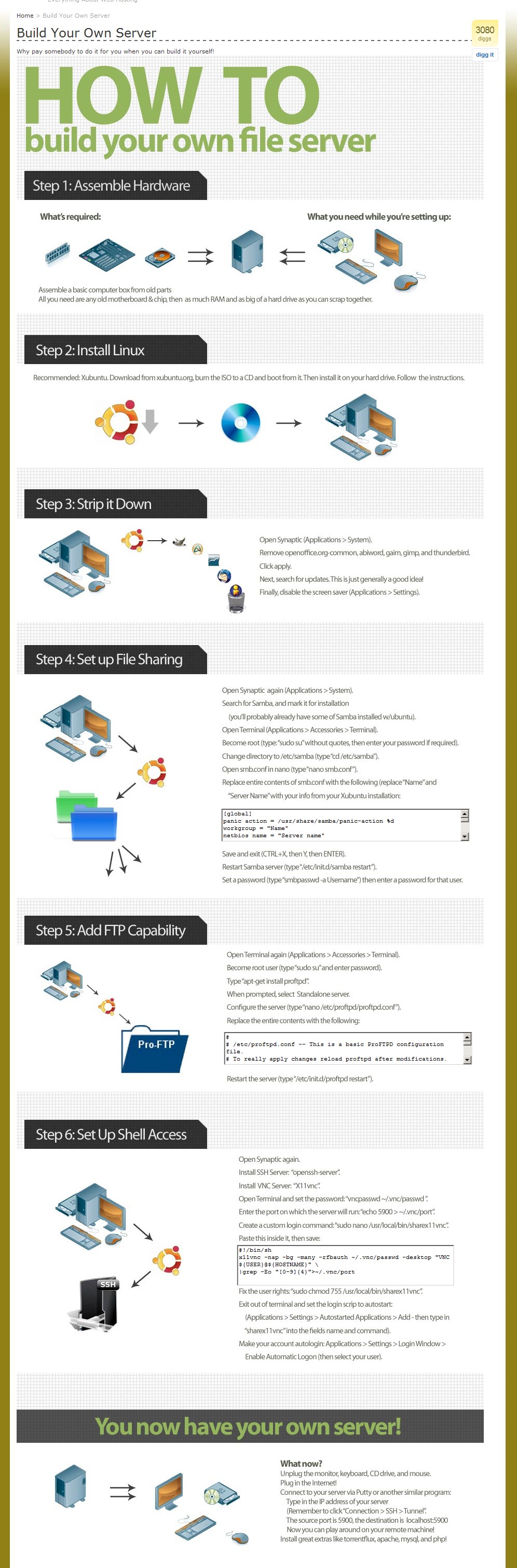
[[File:Setting_up_a_Fileserver.jpeg|thumb|This picture details the ramblings of an incompetent years ago, please do not follow it.]] | [[File:Setting_up_a_Fileserver.jpeg|thumb|This picture details the ramblings of an incompetent years ago, please do not follow it.]] | ||
Revision as of 01:40, 14 February 2014
Need a fileserver that won't face the external internet? Check Home server.
Need to email? Set up a web server? Well, here's some advice. We're gonna try to write this page like you've never done this shit before. It does, however, assume you have at least some basic GNU/Linux knowledge. If you don't, you probably aren't ready for this. You weren't going to set up a server using Windows, were you? Jesus Christ, how horrifying.
A lot of this applies to both a physical machine as well as a VPS setup.
Protecting Your Private Network
Use a DMZ, nigger.
Protecting from DDoS and shit
Use Fail2Ban and perhaps a redundant computer in the DMZ. Also never use passwords, only keyfiles.
Securing your shell
If anyone breaks into your shell, you are FUCKED. They will own your whole server within minutes. There are bots that do nothing but scan for vulnerabilities on random IP addresses all day long, and they will hammer your SSH port like its Natalie Portman's butthole. You need to secure that shit as your first priority, and here's how:
Add a non-root user. Then, while logged in as root, do this:
visudo
Go down to the bit where it says # User privilege specification, and copy the setup for the root line. So, if your non-root user is "faggot," make it look like so:
# User privilege specification root ALL=(ALL) ALL faggot ALL=(ALL) ALL
We are going to use PuTTY in this tutorial because its consistently available on almost all platforms, including GNU/Linux (check your repos) OSX, and Windows. You can also use ssh-keygen for GNU/Linux or something else entirely, but if you already knew that, you probably wouldn't need this page, amirite?
The PuTTY suite includes a program called PuTTYGen. Run PuTTYGen to generate a public/private key pair. Go with SSH-2 DSA, 4096 bits - nobody's gonna crack that shit easily. When done, it will display your public key. Except for the very beginning and very end, it will look like a shitton of gibberish - this is normal. Copy and paste that text into a text file, but omit the last bit that says "dsa-key-########". DO NOT PUT IN A PASSPHRASE. Save the private key.
Open PuTTY and log in as your non-root user. Then do this:
mkdir /home/faggot/.ssh nano /home/faggot/.ssh/authorized_keys
Paste in your public key that you saved as a text file. MAKE SURE IT IS ALL ONE LINE, like so:
ssh-dsa [insanely long string of crap]
And save it.
Now take ownership of it:
chmod 600 ~/.ssh/authorized_keys
DO NOT LOG OUT OF PuTTY YET, but open a second PuTTY session and connect to your server, only this time point PuTTY to your private key file to test it out. If it all goes well, your login will look something like this:
Using username "faggot". Authenticating with public key "dsa-key-########"
Assuming that works, close your previous PuTTY session and do this:
sudo nano /etc/ssh/sshd_config
You can change the SSH port here to a random number - that's optional though, because hacker bots are gonna find it anyhow. But if you do change it don't forget to change it in PuTTY as well.
But DO make the following changes:
PermitRootLogin no PasswordAuthentication no X11Forwarding no UsePAM no
Add the following to the bottom if missing:
UseDNS no AllowUsers faggot
If you have additional users, put a space after "faggot" and add the next user, and so on if you have more.
Save these changes and restart your SSH server. On Debian or other system using a deprecated initscript setup it would be:
sudo /etc/init.d/ssh reload
If you are using systemd, it would be:
sudo systemctl restart sshd
BOOM. Assuming all went well, you have now set up your shell so that 1) "root" cannot log in, 2) ONLY "faggot" can log in, and 3) "faggot" can ONLY log in using their private key file instead of a password. You'll still want to set up and install fail2ban or similar to secure things further.
Oh, and don't lose that private key file. You cannot recreate it, so losing it means you are doomed. Back it up in multiple places. You may wish to place a copy on a floppy drive (if you're a time-traveller from 1995) or USB stick as well, for safekeeping.
Securing your shell even more (and everything else)
Even with your shell secured, its still gonna get hammered, and that's going to get irritating quick. Given enough time, even your super-secret keyfile can eventually be guessed. Well, guess what? You can ban the SHIT out of those bots with fail2ban.
fail2ban monitors your log files (any of them, not just SSH). If it sees too many login failures, it bans the offending IP for as long as you configure it to. It won't prevent a distributed brute-force attack, but it will help a LOT.
- How To Protect SSH with fail2ban on Debian 7
- How To Protect SSH with fail2ban on CentOS 6
- How To Protect SSH with fail2ban on Ubuntu 12.04
Please note that if you are going to install iRedMail (below), it will install and configure fail2ban for you. You may still wish to tweak its settings though.
Setting Up Email and web server, the EASY way
See also: Email
Want to use your own email server to avoid the NSA? Good call! But setting up email servers can be pretty complicated. Assuming you mostly don't know what the hell you are doing, and assuming you're already secured your system per above, have a peek at iRedMail. iRedMail is an automated email and web server setup package. It works best if installed on a FRESH system - if you're already fumbled around with Apache and/or dovecot and/or postfix and failed, wipe your shit and start over with iRedMail. It will install and configure Postfix, Dovecot, Apache, and MySQL. It also installs and configures fail2ban and iptables. It includes spam filtering and greylisting. It just works. Its pretty awesome.
You will, however, still need to manually set up your DNS records (MX, SPF, and DKIM). Refer to the Email article for more on this.
If you want to get fancy and replace MySQL with MariaDB, or replace Apache with, say, Nginx, you can do that after you set up iRedMail, but any breakage is up to you to fix.
External links
Linode Library - Good beginner tutorials.